13 11 2015
New Published CompTIA SY0-401 Exam Dumps Free Download from Braindump2go! (81-90)
COMPTIA NEWS: SY0-401 Exam Questions has been Updated Today! Get Latest SY0-401 VCE and SY0-401 PDF Instantly! Welcome to Download the Newest Braindump2go SY0-401 VCE&SY0-401 PDF Dumps: http://www.braindump2go.com/sy0-401.html (1220 Q&As)
2015 CompTIA SY0-401 Certification Exam is coming! Getting a Laest SY0-401 Practice Test is very important for an Exam Candiate! Braindump2go New Updated SY0-401 Exam Questions Well Formatted in PDF and VCE versions, providing you convenience and excellence both at the same time! Free Questions and Answer are provided Following:
Exam Code: SY0-401
Exam Name: CompTIA Security+
Certification Provider: CompTIA
Corresponding Certification: CompTIA Security+
SY0-401 Dump,SY0-401 PDF,SY0-401 VCE,SY0-401 Braindump,SY0-401 Study Guide,SY0-401 Study Guide PDF,SY0-401 Objectives,SY0-401 Practice Test,SY0-401 Practice Exam,SY0-401 Performance Based Questions,SY0-401 Exam Questions,SY0-401 Exam Dumps,SY0-401 Exam PDF,SY0-401 Dumps Free,SY0-401 Dumps PDF

QUESTION 81
If you don’t know the MAC address of a Linux-based machine, what command-line utility can you use to ascertain it?
A. macconfig
B. ifconfig
C. ipconfig
D. config
Answer: B
Explanation:
To find MAC address of a Unix/Linux workstation, use ifconfig or ip a.
QUESTION 82
An organization does not want the wireless network name to be easily discovered. Which of the following software features should be configured on the access points?
A. SSID broadcast
B. MAC filter
C. WPA2
D. Antenna placement
Answer: A
Explanation:
Numerous networks broadcast their name (known as an SSID broadcast) to reveal their presence.
QUESTION 83
A security architect wishes to implement a wireless network with connectivity to the company’s internal network. Before they inform all employees that this network is being put in place, the architect wants to roll it out to a small test segment. Which of the following allows for greater secrecy about this network during this initial phase of implementation?
A. Disabling SSID broadcasting
B. Implementing WPA2 – TKIP
C. Implementing WPA2 – CCMP
D. Filtering test workstations by MAC address
Answer: A
Explanation:
Network administrators may choose to disable SSID broadcast to hide their network from unauthorized personnel. However, the SSID is still needed to direct packets to and from the base station, so it’s a discoverable value using a wireless packet sniffer. Thus, the SSID should be disabled if the network isn’t for public use.
QUESTION 84
While previously recommended as a security measure, disabling SSID broadcast is not effective against most attackers because network SSIDs are:
A. no longer used to authenticate to most wireless networks.
B. contained in certain wireless packets in plaintext.
C. contained in all wireless broadcast packets by default.
D. no longer supported in 802.11 protocols.
Answer: B
Explanation:
The SSID is still required for directing packets to and from the base station, so it can be discovered using a wireless packet sniffer.
QUESTION 85
A company provides secure wireless Internet access for visitors and vendors working onsite. Some of the vendors using older technology report that they are unable to access the wireless network after entering the correct network information. Which of the following is the MOST likely reason for this issue?
A. The SSID broadcast is disabled.
B. The company is using the wrong antenna type.
C. The MAC filtering is disabled on the access point.
D. The company is not using strong enough encryption.
Answer: A
Explanation:
When the SSID is broadcast, any device with an automatic detect and connect feature is able to see the network and can initiate a connection with it. The fact that they cannot access the network means that they are unable to see it.
QUESTION 86
Which of the following best practices makes a wireless network more difficult to find?
A. Implement MAC filtering
B. UseWPA2-PSK
C. Disable SSID broadcast
D. Power down unused WAPs
Answer: C
Explanation:
Network administrators may choose to disable SSID broadcast to hide their network from unauthorized personnel. However, the SSID is still needed to direct packets to and from the base station, so it’s a discoverable value using a wireless packet sniffer.
Thus, the SSID should be disabled if the network isn’t for public use.
QUESTION 87
Jane, the security administrator, sets up a new AP but realizes too many outsiders are able to connect to that AP and gain unauthorized access.
Which of the following would be the BEST way to mitigate this issue and still provide coverage where needed? (Select TWO).
A. Disable the wired ports
B. Use channels 1, 4 and 7 only
C. Enable MAC filtering
D. Disable SSID broadcast
E. Switch from 802.11a to 802.11b
Answer: CD
Explanation:
Network administrators may choose to disable SSID broadcast to hide their network from unauthorized personnel. However, the SSID is still needed to direct packets to and from the base station, so it’s a discoverable value using a wireless packet sniffer. Thus, the SSID should be disabled if the network isn’t for public use.
A MAC filter is a list of authorized wireless client interface MAC addresses that is used by a WAP to block access to all unauthorized devices.
QUESTION 88
Which of the following wireless security technologies continuously supplies new keys for WEP?
A. TKIP
B. Mac filtering
C. WPA2
D. WPA
Answer: A
Explanation:
TKIP is a suite of algorithms that works as a “wrapper” to WEP, which allows users of legacy WLAN equipment to upgrade to TKIP without replacing hardware. TKIP uses the original WEP programming but “wraps” additional code at the beginning and end to encapsulate and modify it.
QUESTION 89
A network administrator has been tasked with securing the WLAN. Which of the following cryptographic products would be used to provide the MOST secure environment for the WLAN?
A. WPA2 CCMP
B. WPA
C. WPA with MAC filtering
D. WPA2 TKIP
Answer: A
Explanation:
CCMP is the standard encryption protocol for use with the WPA2 standard and is much more secure than the WEP protocol and TKIP protocol of WPA. CCMP provides the following security services:
Data confidentiality; ensures only authorized parties can access the information Authentication; provides proof of genuineness of the user Access control in conjunction with layer management
Because CCMP is a block cipher mode using a 128-bit key, it is secure against attacks to the 264 steps of operation.
QUESTION 90
An access point has been configured for AES encryption but a client is unable to connect to it. Which of the following should be configured on the client to fix this issue?
A. WEP
B. CCMP
C. TKIP
D. RC4
Answer: B
Explanation:
CCMP is an encryption protocol designed for Wireless LAN products that implement the standards of the IEEE 802.11i amendment to the original IEEE 802.11 standard. CCMP is an enhanced data cryptographic encapsulation mechanism designed for data confidentiality and based upon the Counter Mode with CBC-MAC (CCM) of the AES standard.
Braindump2go Promises All our customers: 100% All Exams Pass Or Full Money Back! Our experts have complied the fail proof SY0-401 Exam content to help all candidates pass your SY0-401 certification exam easily in the first attempt and score the top possible grades too.Do you want to sucess? Come to Braindump2go and our experts team will tell you what you need to do! SY0-401 Exam Dumps Full Version Download:
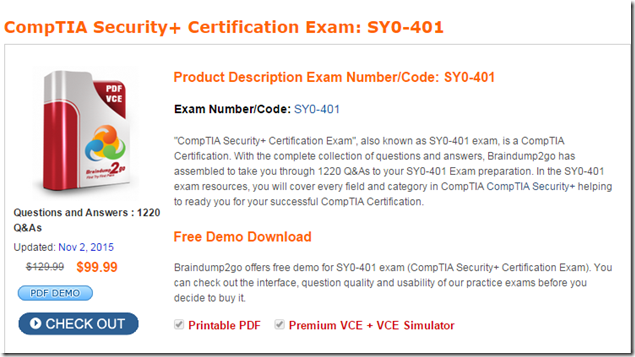
FREE DOWNLOAD: NEW UPDATED SY0-401 PDF Dumps & SY0-401 VCE Dumps from Braindump2go: http://www.braindump2go.com/sy0-401.html (1220 Q&A)
[FREE]Braindump2go SY0-401 Exam Ref Download (71-80) New SY0-401 Exam Version Released By Braindump2go Recently For Free Download (91-100)
Comments are currently closed.