22 04 2014
2014 Cisco 100-101 Exam Dump(41-50)
QUESTION 41
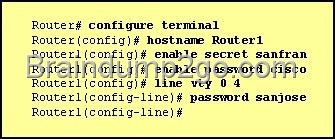
Refer to the exhibit. The network administrator made the entries that are shown and then saved the configuration. From a console connection, what password or password sequence is required for the administrator to access privileged mode on Router1?
A. cisco
B. sanfran
C. sanjose
D. either cisco or sanfran
E. either cisco or sanjose
F. sanjose and sanfran
Answer: B
Explanation:
The enable secret password takes precedence over the enable password, so sanfran will be used.
QUESTION 42
The following commands are entered on the router:
Burbank(config)# enable secret fortress
Burbank(config)# line con 0
Burbank(config-line)# login
Burbank(config-line)# password n0way1n
Burbank(config-line)# exit
Burbank(config)# service password-encryption
What is the purpose of the last command entered?
A. to require the user to enter an encrypted password during the login process
B. to prevent the vty, console, and enable passwords from being displayed in plain text in the configuration files
C. to encrypt the enable secret password
D. to provide login encryption services between hosts attached to the router
Answer: B
QUESTION 43
What is the effect of using the service password-encryption command?
A. Only the enable password will be encrypted.
B. Only the enable secret password will be encrypted.
C. Only passwords configured after the command has been entered will be encrypted.
D. It will encrypt the secret password and remove the enable secret password from the configuration.
E. It will encrypt all current and future passwords.
Answer: E
Explanation:
Encryption further adds a level of security to the system as anyone having access to the database of passwords cannot reverse the process of encryption to know the actual passwords which isn’t the case if the passwords are stored simply.
QUESTION 44
An administrator has connected devices to a switch and, for security reasons, wants the dynamically learned MAC addresses from the address table added to the running configuration. What must be done to accomplish this?
A. Enable port security and use the keyword sticky.
B. Set the switchport mode to trunk and save the running configuration.
C. Use the switchport protected command to have the MAC addresses added to the configuration.
D. Use the no switchport port-security command to allow MAC addresses to be added to the configuration.
Answer: A
Explanation:
One can configure MAC addresses to be sticky. These can be dynamically learned or manually configured, stored in the address table, and added to the running configuration. If these addresses are saved in the configuration file, the interface does not need to dynamically relearn them when the switch restarts, hence enabling security as desired.
QUESTION 45
A company has placed a networked PC in a lobby so guests can have access to the corporate directory. A security concern is that someone will disconnect the directory PC and re-connect their laptop computer and have access to the corporate network. For the port servicing the lobby, which three configuration steps should be performed on the switch to prevent this? (Choose three.)
A. Enable port security.
B. Create the port as a trunk port.
C. Create the port as an access port.
D. Create the port as a protected port.
E. Set the port security aging time to 0.
F. Statically assign the MAC address to the address table.
G. Configure the switch to discover new MAC addresses after a set time of inactivity.
Answer: ACF
Explanation:
If port security is enabled and the port is only designated as access port, and finally static MAC address is assigned, it ensures that even if a physical connection is done by taking out the directory PC and inserting personal laptop or device, the connection cannot be made to the corporate network, hence ensuring safety.
QUESTION 46
Why would a network administrator configure port security on a switch?
A. to prevent unauthorized Telnet access to a switch port
B. to prevent unauthorized hosts from accessing the LAN
C. to limit the number of Layer 2 broadcasts on a particular switch port
D. block unauthorized access to the switch management interfaces
Answer: B
Explanation:
You can use the port security feature to restrict input to an interface by limiting and identifying MAC addresses of the stations allowed to access the port. When you assign secure MAC addresses to a secure port, the port does not forward packets with source addresses outside the group of defined addresses. If you limit the number of secure MAC addresses to one and assign a single secure MAC address, the workstation attached to that port is assured the full bandwidth of the port. If a port is configured as a secure port and the maximum number of secure MAC addresses is reached, when the MAC address of a station attempting to access the port is different from any of the identified secure MAC addresses, a security violation occurs. Also, if a station with a secure MAC address configured or learned on one secure port attempts to access another secure port, a violation is flagged.
QUESTION 47
How can you ensure that only the MAC address of a server is allowed by switch port Fa0/1?
A. Configure port Fa0/1 to accept connections only from the static IP address of the server.
B. Configure the server MAC address as a static entry of port security.
C. Use a proprietary connector type on Fa0/1 that is incomputable with other host connectors.
D. Bind the IP address of the server to its MAC address on the switch to prevent other hosts from spoofing
the server IP address.
Answer: B
Explanation:
When the MAC address is configured as static entry, no other address is allowed.
QUESTION 48
Which IP addresses are valid for hosts belonging to the 10.1.160.0/20 subnet? (Choose three.)
A. 10.1.168.0
B. 10.1.176.1
C. 10.1.174.255
D. 10.1.160.255
E. 10.1.160.0
F. 10.1.175.255
Answer: ACD
Explanation:
All IP address in IP ranges between : 10.1.160.1 and 10.1.175.254 are valid as shown below
Address: 10.1.160.0 00001010.00000001.1010 0000.00000000 Netmask:255.255.240.0 = 2011111111.11111111.1111 0000.00000000 Wildcard:0.0.15.25500000000.00000000.0000 1111.11111111 Which implies that
Network: 10.1.160.0/20 00001010.00000001.1010 0000.00000000 HostMin:10.1.160.100001010.00000001.1010 0000.00000001 HostMax:10.1.175.25400001010.00000001.1010 1111.11111110 Broadcast:10.1.175.25500001010.00000001.1010 1111.11111111
QUESTION 49
If a host experiences intermittent issues that relate to congestion within a network while remaining connected, what could cause congestion on this LAN?
A. half-duplex operation
B. broadcast storms
C. network segmentation
D. multicasting
Answer: B
Explanation:
A broadcast storm can consume sufficient network resources so as to render the network unable to transport normal traffic.
QUESTION 50
Given an IP address of 192.168.1.42 255.255.255.248, what is the subnet address?
A. 192.168.1.8/29
B. 192.168.1.32/27
C. 192.168.1.40/29
D. 192.168.1.16/28
E. 192.168.1.48/29
Answer: C
Explanation:
248 mask uses 5 bits (1111 1000)
42 IP in binary is (0010 1010)
The base subnet therefore is the lowest binary value that can be written without changing the output of an AND operation of the subnet mask and IP …
1111 1000 AND
0010 1010 equals
0010 1000 – which is .40
/24 is standard class C mask.
adding the 5 bits from the .248 mask gives /29
If you want to pass the Cisco 100-101 Exam sucessfully, recommend to read latest Cisco 100-101 Dump full version.
2014 Cisco 100-101 Exam Dump(31-40) 2014 Cisco 100-101 Exam Dump(51-60)

Comments are currently closed.